Enable DNSSEC in Namebase DNS
under review
Rithvik Vibhu
As of now, the only way for any Namebase user to set up a secure website is to host their own DNS server and enable DNSSEC on it. Enabling it on Namebase DNS helps everyone to set up secure websites without having to maintain their own cloud server.
This feedback post focuses on part 1 (of 3) below.
One idea on how Namebase can support in stages:
1) Enable DNSSEC in Namebase DNS
This lets the tech savvy people manually set up https without having to spin up own nameservers.
Namebase DNS is based on powerdns so it's essentially a toggle from OFF to ON (but you guys would probably want to test it a bit I think ;)) - shouldn't take a lot of effort/time.
2) Set up DNSSEC for newly registered names
Automatically add DS records along with the ns1 and ns2 default records being set pointing to nb dns.
Again, will need a bit of code to get the value for the record first, but doable.
At this point, anyone hosting a site somewhere (heroku or wherever) can set up https without a lot of work (but it's still manual process).
3) Add SSL support to thr Sia Gateway and set the TLSA record in Namebase DNS
Now to get https on dlinks, the gateway should use an SSL certificate which changes for every domain. This may take work, and the community can help if open source contributions to make this work will be accepted.
Dlinks will also need a small change to add 1 extra TLSA record, again, not much work.
At this stage, dlinks will automatically have https.
S
Sebastian Rasor
I'd also love for Namebase to support these records or even better, provide an automated DNSSEC service in a similar manner to other authoritative DNS providers.
Currently, Namebase is holding back security on Handshake by not supporting DNSSEC. On https://handshake.org, Handshake is described as a "Decentralized naming and certificate authority." The way this decentralized certificate authority works is by following a DNSSEC chain of trust down from the Handshake blockchain to a given domain, whether it be a TLD, second-level domain, or a subdomain of a second-level domain with its own delegated zone.
The best solution going forward would be for Namebase to add a per-name toggle to enable automatic invisible signing of all records currently existing, modified, or added in the future, and to enable this toggle by default on all newly registered names. This is understandably a large undertaking, so in the meantime it would be acceptable to also allow for DNSKEY, RRSID, and TLSA records to allow users to manually sign their own records using Namebase's nameservers.
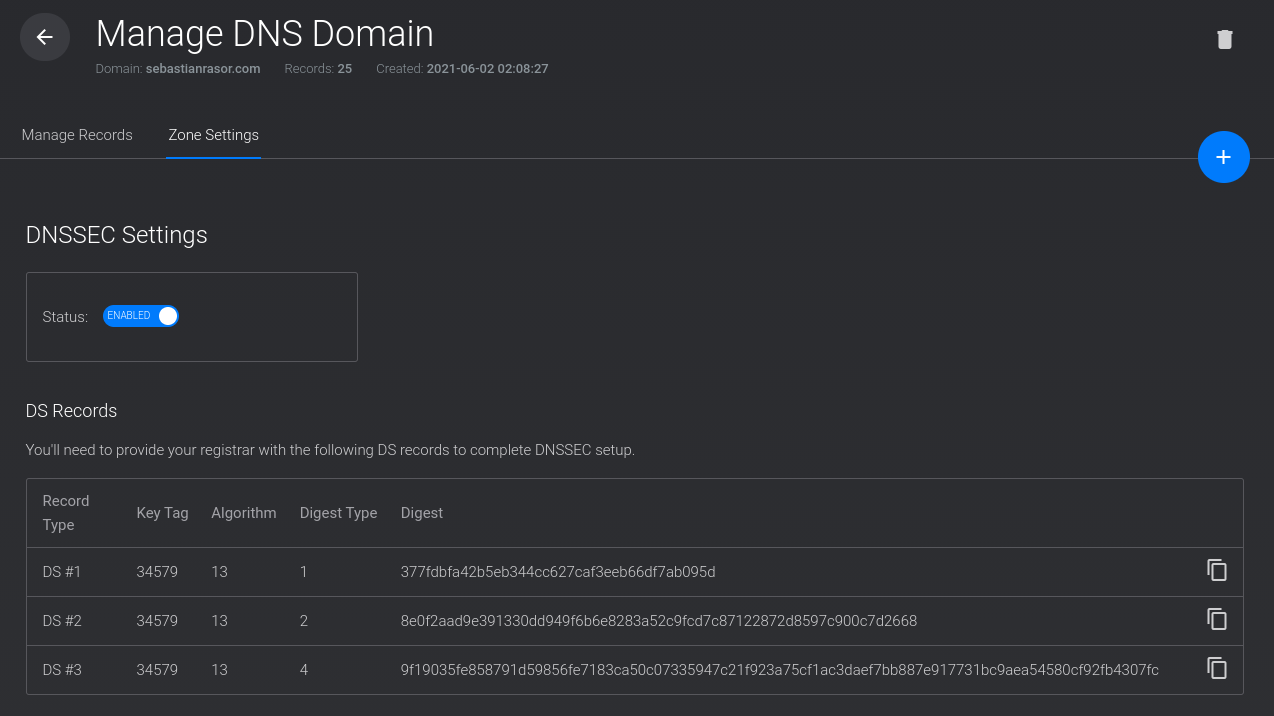
I've attached an image of how we handle DNSSEC at Vultr: you enable a toggle and add records to your registrar. Since the Namebase nameservers are only in use by those already registered on Namebase, the DS records could be automatically added to the blockchain by Namebase with no user interaction required other than simply flipping the toggle. There is the issue, of course, of a DNSSEC enabled site being inaccessible until an Urkel tree update, which could take up to 6 hours. In this case, it would make sense to not start automatically signing records until the tree has been updated.
Johnny Wu
under review